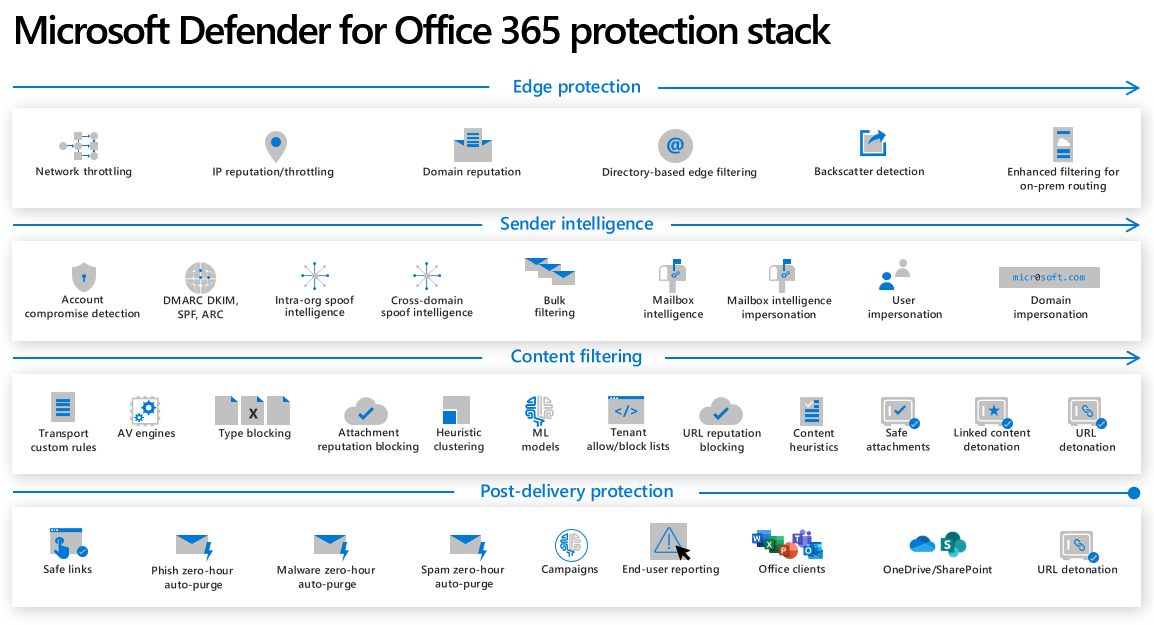
Step-by-step threat protection stack in Microsoft Defender for Office 365 - Office 365 | Microsoft Docs

Review architecture requirements and planning concepts for Microsoft Defender for Office 365 | Microsoft Docs
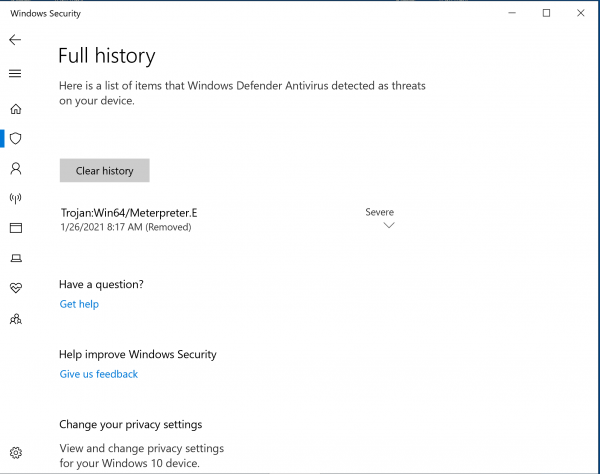
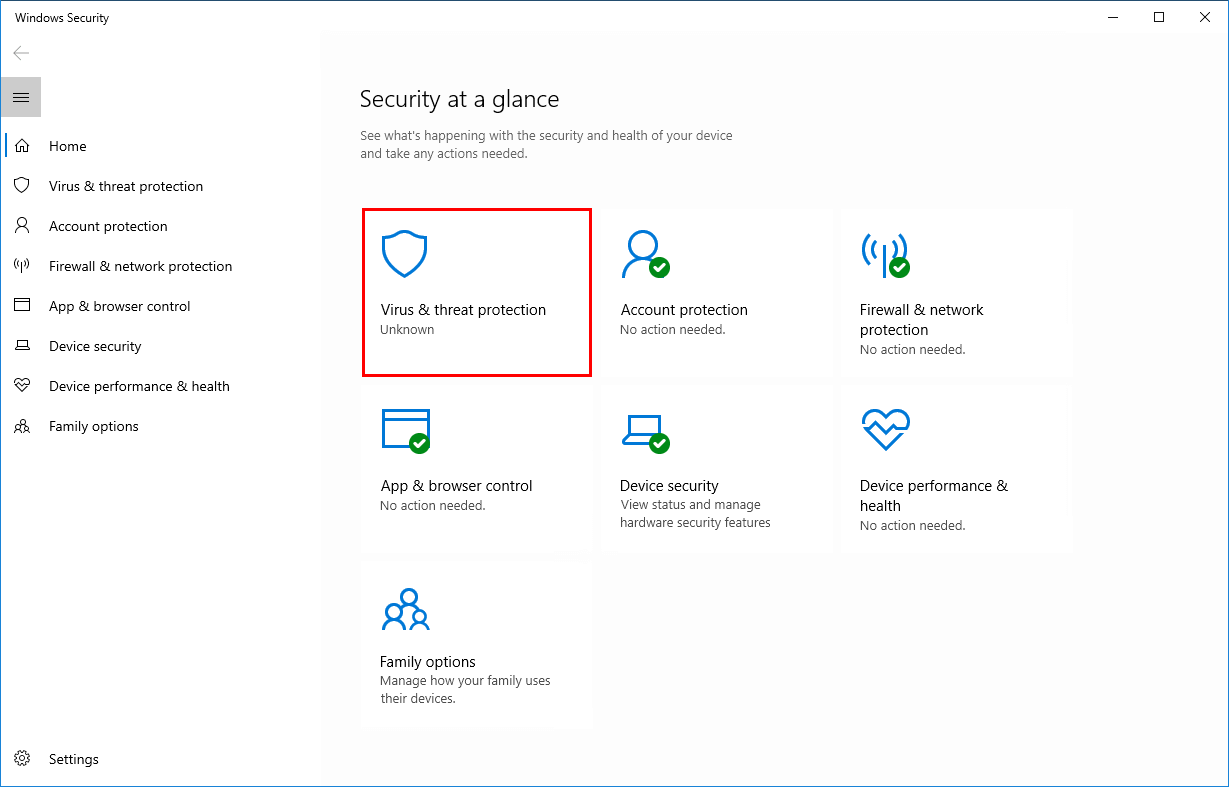
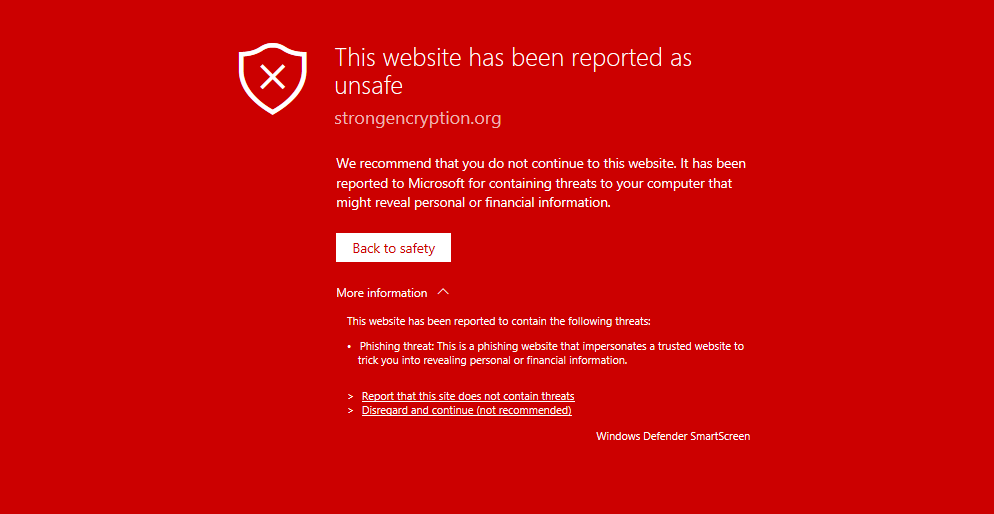
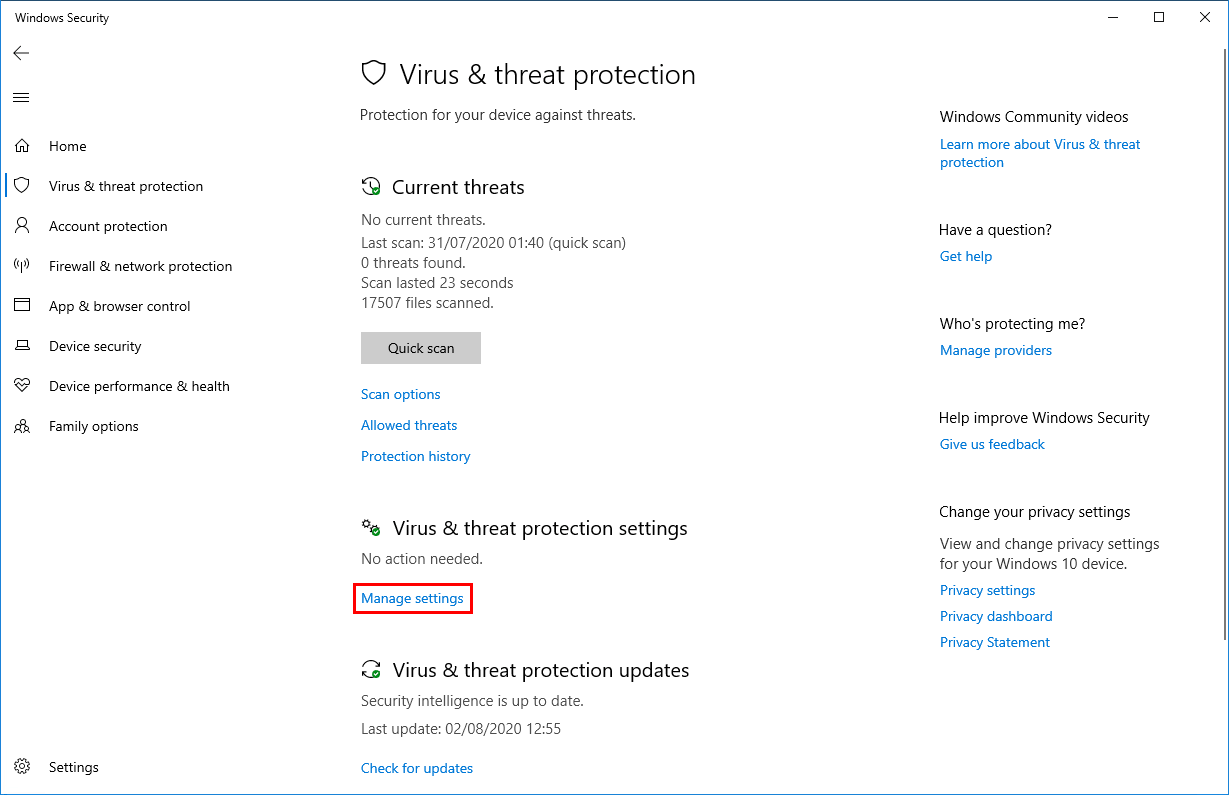
Bypassing Windows Defender with Environmental Decryption Keys - Secarma: Penetration Testing and Cybersecurity Company